In a move that has sparked intense debate across Hacker News and the wider Linux community, System76 has officially addressed the impact of new System76 age verification laws on the technology sector. As California’s AB 1043 (Digital Age Assurance Act) and New York’s S8102A go into effect this year, the manufacturer of Pop!_OS finds itself at the forefront of a regulatory battle that threatens the very core of user privacy and digital freedom.
The Challenge of AB 1043 and New York S8102A
The digital landscape changed overnight as governments implemented stricter mandates to protect minors online. While well-intentioned, these laws require platforms to verify the age of every user before granting access to “harmful” content. For a hardware manufacturer like System76, the challenge is twofold: complying with the law while refusing to build invasive tracking into their operating systems.
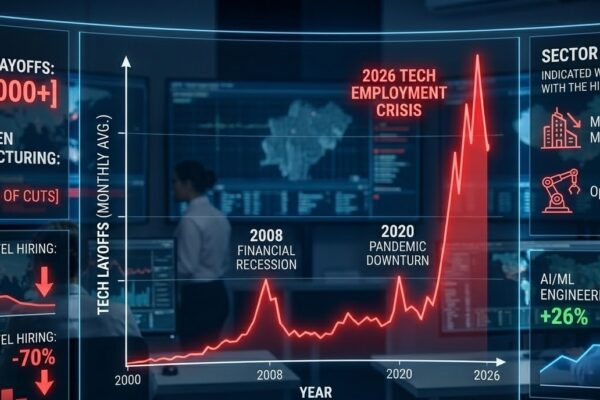
Recent 2026 statistics show that over 30 countries now enforce some form of digital age gating. However, the American mandates—specifically California’s AB 1043—are the first to suggest that the operating system itself should act as the “identity layer.”
Why System76 Fears a “Nerfed Internet”
System76 CEO Carl Richell recently warned that if Linux distributions do not provide an OS-level “age signal,” users might face a “nerfed internet.” This term describes a scenario where websites automatically block Linux users or provide a restricted experience because the browser cannot “vouch” for the user’s age without proprietary verification APIs.
The Technical Implications for Linux Users
From a technical perspective, the System76 age verification laws create significant hurdles for open-source development:
- Integration Complexity: Modern OS kernels were not designed to store and broadcast verified ID tokens.
- Security Vulnerabilities: Creating a “verification gate” provides a single point of failure for hackers to target sensitive user data.
- Privacy Erosion: System76 refuses to implement “phone home” telemetry, which many age verification providers require.
- Compatibility: Many open-source tools may break if they are suddenly required to handshake with government-approved identity servers.
Expert Insight: “Privacy is not a feature; it is a fundamental right in the System76 ecosystem,” says security researcher Elena Vance. “The push for age gates at the OS level is essentially a push for a digital ID.”
System76’s Roadmap: Privacy-Preserving Compliance
How does a company like System76 comply without betraying its users? The company is currently exploring “Zero-Knowledge Proof” (ZKP) technologies. This would allow a user to prove they are over 18 without ever revealing their actual birthdate, name, or address to the website they are visiting.
Industry Comparison: Handling Age Gates
| Feature | Windows/macOS Approach | System76 / Pop!_OS Approach |
| Data Collection | Centralized Account Linking | Localized Privacy Tokens |
| User Identity | Verified via Credit Card/ID | Zero-Knowledge Proofs |
| Compliance | Deep OS-Level Integration | Opt-in Browser Signal |
For more on how these regulations are shifting, you can read the latest updates from the Electronic Frontier Foundation (EFF), which has been vocal about the dangers of mandatory age verification.
The Future of Open Source and Digital Freedom
The current debate over System76 age verification laws is a crucial moment for the industry. System76’s proactive stance has opened vital dialogues about how we can protect minors without turning the internet into a surveillance-heavy environment.
Recommendations for Tech Professionals
Based on the System76 roadmap, companies facing similar regulatory pressure should:
- Prioritize Local Verification: Store verification signals locally on the device, not in the cloud.
- Engage with Lawmakers: Advocate for “privacy-by-design” in future legislative drafts.
- Collaborate on Standards: Work with the Linux Foundation to create unified, non-invasive compliance protocols.
Conclusion: A Call to Action
As the tech industry evolves, the conversation around System76 age verification laws remains essential. System76 continues to prove that it is possible to maintain open-source principles while navigating a complex regulatory world.
What are your thoughts on age verification laws? Can we protect children without sacrificing the privacy of Linux users? Share your perspective in the comments below.